Cybersecurity is about comprehensive risk management
Security risk management
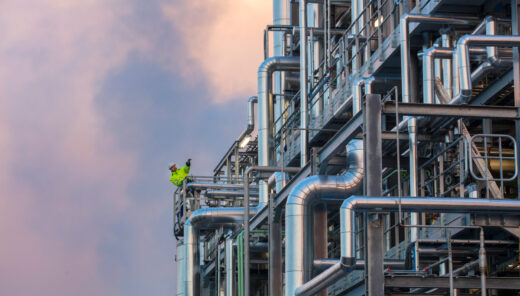
Cybersecurity is about comprehensive risk management. Identifying and being aware of the risks allows you to prepare for them with clear operating plans and documentation. We offer a range of methods for assessing security risks.
Risk awareness
The importance of cybersecurity is often revealed when something bad happens unexpectedly. Cyberattacks are being increasingly used as tools in global politics, ransomware is becoming more and more common and computer viruses spread throughout the globe. If you are not aware of information security risks, you cannot react fast enough to incidents.
The proactive management of cyber risks improves information flow. In practice, it means having detailed documentation of all the inter-process connections in your facility, for example. In fact, cyber risk management is all about awareness and operating plans. The world is constantly changing and technologies are rapidly developing, which is why preparing for cyber risks requires constant development work.
Technical information security risks assessment
Ideally, the assessment of cybersecurity risks should be started as early as the pre-planning stage, allowing the risk assessments to steer equipment procurement as well. That being said, cyber risk assessment can also be carried out on existing facilities. One of our assessment tools is technical information security risks assessment, which focuses on assessing the risks of the production environment.
Cybersecurity survey
One way of assessing cyber risks is through a discussion-based security survey. In the survey, we go over things like your facility’s general situation, your current information security policy and your data governance with you, highlighting notable issues and thus helping your management with the decision-making related to risk management. The cybersecurity survey is part of Safety Index, a risk and security management tool developed by Sweco.
Information security monitoring
Information security is always a process. The world is rapidly changing, which is why it is important for information security practices to also constantly develop to tackle actual threats. We can help you follow international and national legislation, sector-specific recommendations and future trends. When it comes to information security, it is important to also consider the company’s internal information security policy and choose the most suitable measures for developing data governance and protecting the company’s business against cyber threats.
Cris Puchner
Head of SecuritySanna-Maria Järvensivu
Security and Safety Specialist